- Product
- Use Cases
- Resources
EducationTemplatesSuccess Stories
- Pricing
- Product
- Use Cases
- Resources
EducationTemplatesSuccess Stories
- Pricing



Trusted by 5K+ teams of all sizes
|
4.8/5 (180+ reviews)
“Exceptional Tool for Business Knowledge”
Whale is excellent to document and organize business knowledge. Their AI makes it even easier!
“Whale Keeps Work Organized and Teams Confident”
Whale unifies documentation, training, and reviews in one ecosystem.
“Screen Recorder Transformed Our Productivity”
All features are excellent, but the Screen Recorder has boosted productivity for our company.
“User-Friendly Platform with Great Features”
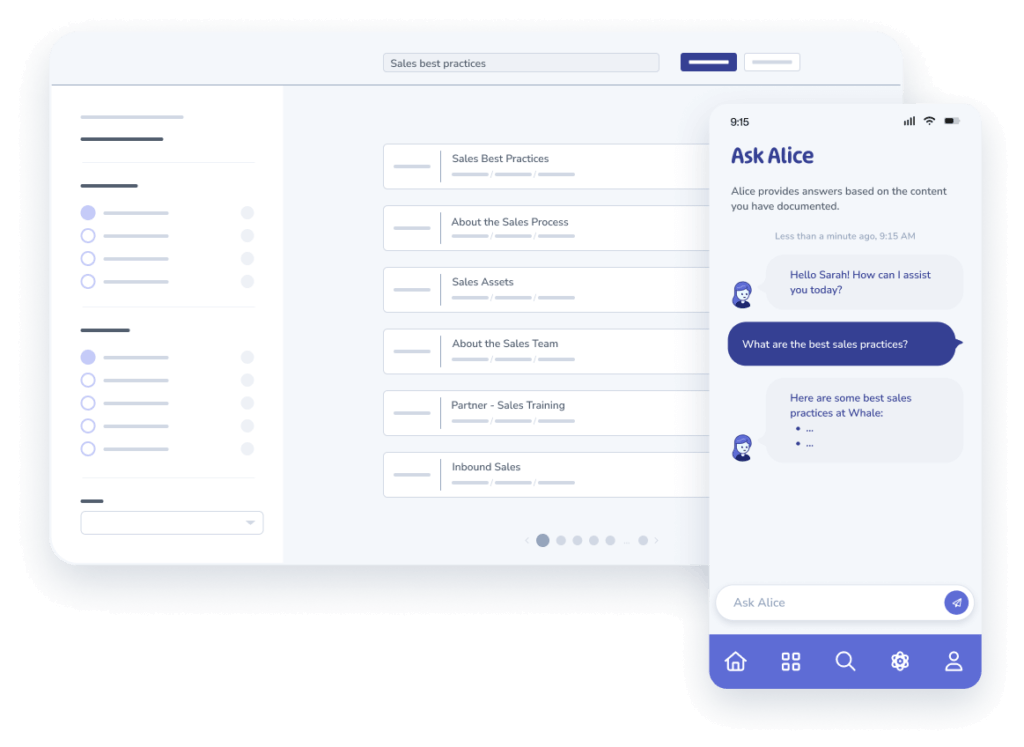
Whale is very user-friendly. "Alice" has been a game changer, makes finding information effortless.
“Intuitive, fresh and easy!”
Whale's clean layout makes building and navigating SOPs a breeze.
“Productivity Unleashed!”
Managing and write SOP versions, assign them, track progress through a dashboard, and automate revision tracking.
“My company utilizes Whale for our SOP’s and FAQ’s.”
Everything is very easy to locate and the search bar is my favorite feature. When I need a quick answer I turn to Whale to find what I am looking for.
“Whale Streamlined Our Processes and Boosted Team Onboarding”
Whale transformed how we manage internal processes. Documenting SOPs is fast and we can build and share training materials in minutes, making onboarding significantly more efficient.
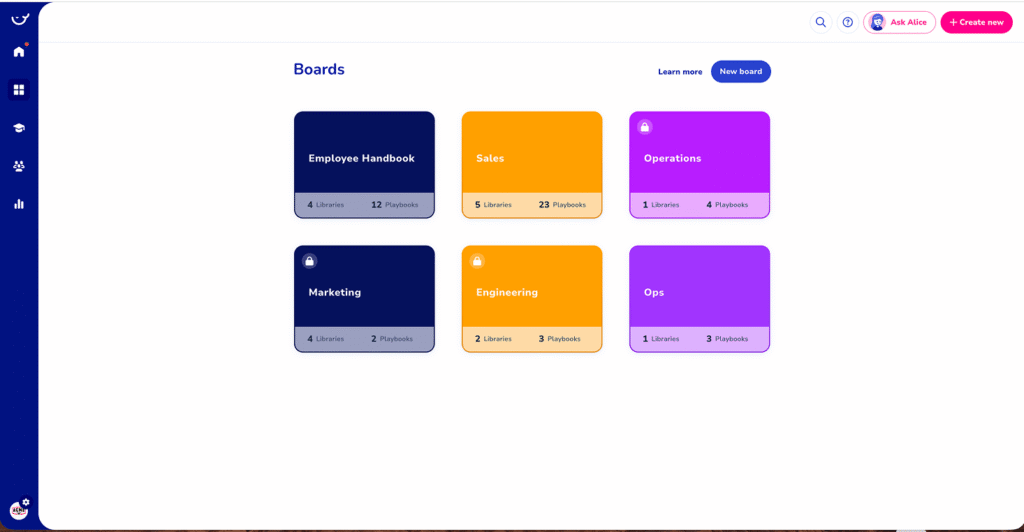
“Whale Keeps Department Training Organized with Boards, Libraries, and Playbooks”
Boards, Libraries, and Playbooks keep training organized by department, so you can generate videos, SOPs, quizzes, and more for each topic.
“Streamlines Documentation with Ease”
I use Whale for company handbooks, regulations, how-to's, and manuals, all on one platform. The step-by-step screen recorder auto-captures screenshots and saves me about an hour per guide.
“Effortlessly Streamlines Team Training with Solid Support”
Whale supports training my merchandising teams with AI and video features that break down training step by step. Creating training flows is easy, and quizzes ensure the material lands.
“Effortless SOP Management with Stellar AI Search”
Whale centralizes all our SOPs with standard formatting and makes them easy to find — especially with the fast AI search across thousands of documents.